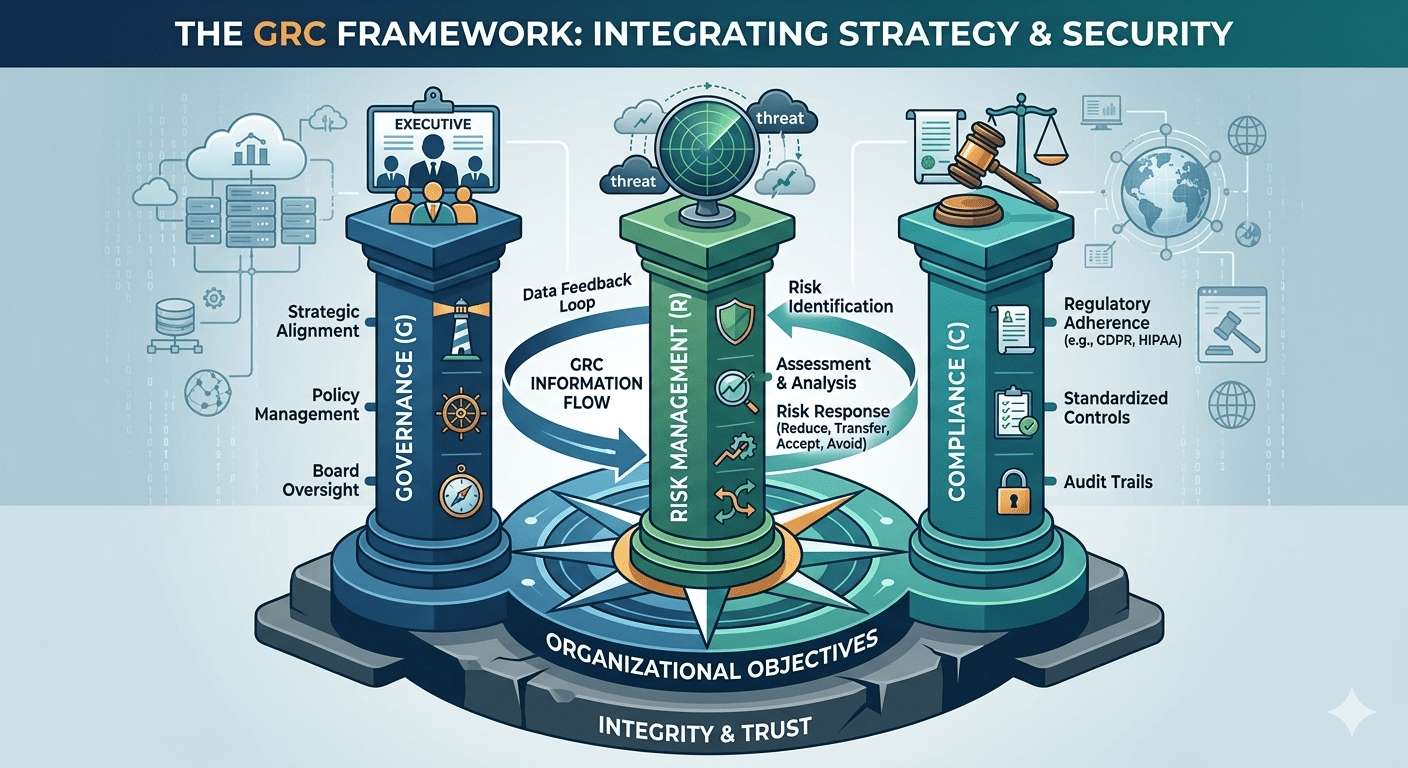
In the world of cybersecurity, many people focus on the “cool” stuff: firewalls, ethical hacking, and threat hunting. But for a business to actually survive and thrive in a digital economy, it needs a brain to coordinate those muscles. That brain is GRC. If you are pursuing a certification like the ISC2 SSCP or CISSP, […]
SSCP Day 17: Access at Your Fingertips: The Discretionary Power of DAC
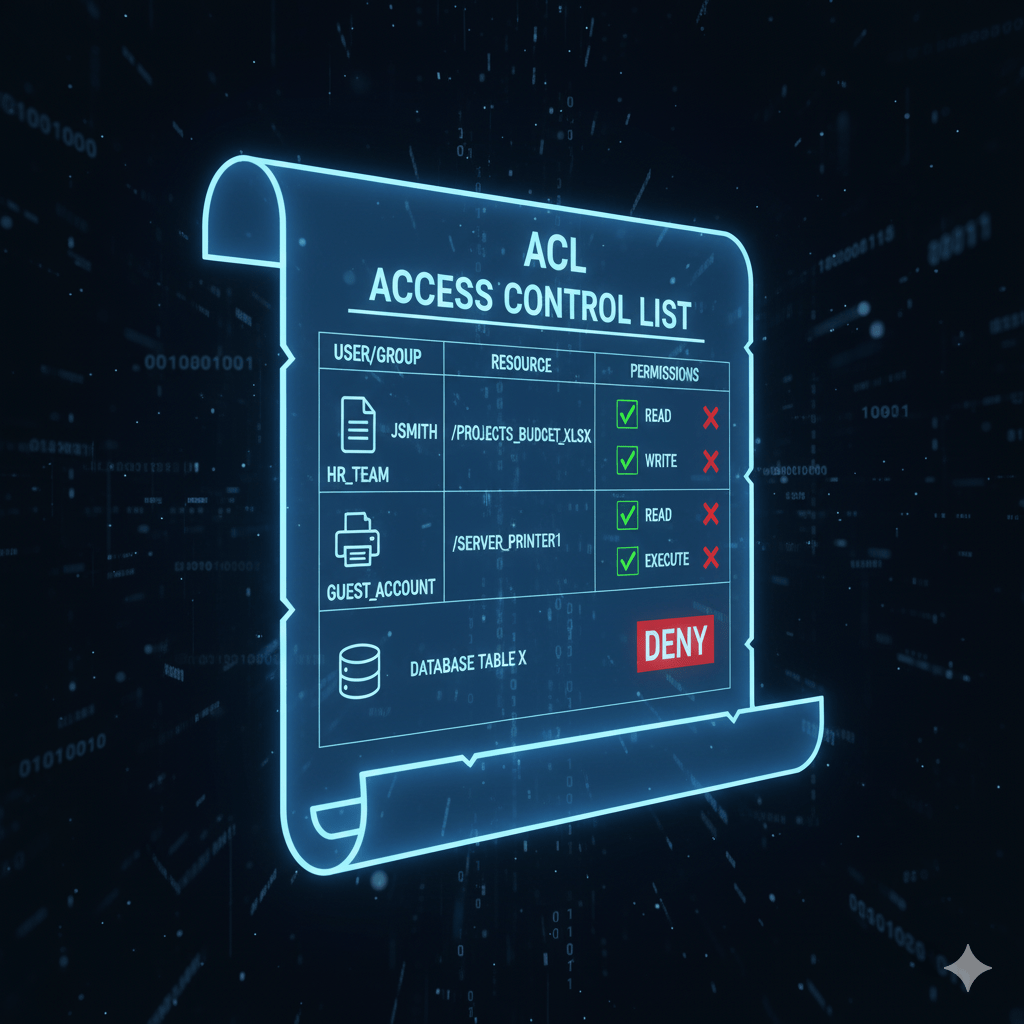
In the world of authorization models, Discretionary Access Control (DAC) is the most common, flexible, and widely used model in commercial operating systems, such as Windows, macOS, and Linux. DAC is a core concept in SSCP Domain 2: Security Operations and Administration because it governs how most users interact with files and resources every day. […]
SSCP Day 16: Security’s Straitjacket: Mandatory Access Control (MAC)
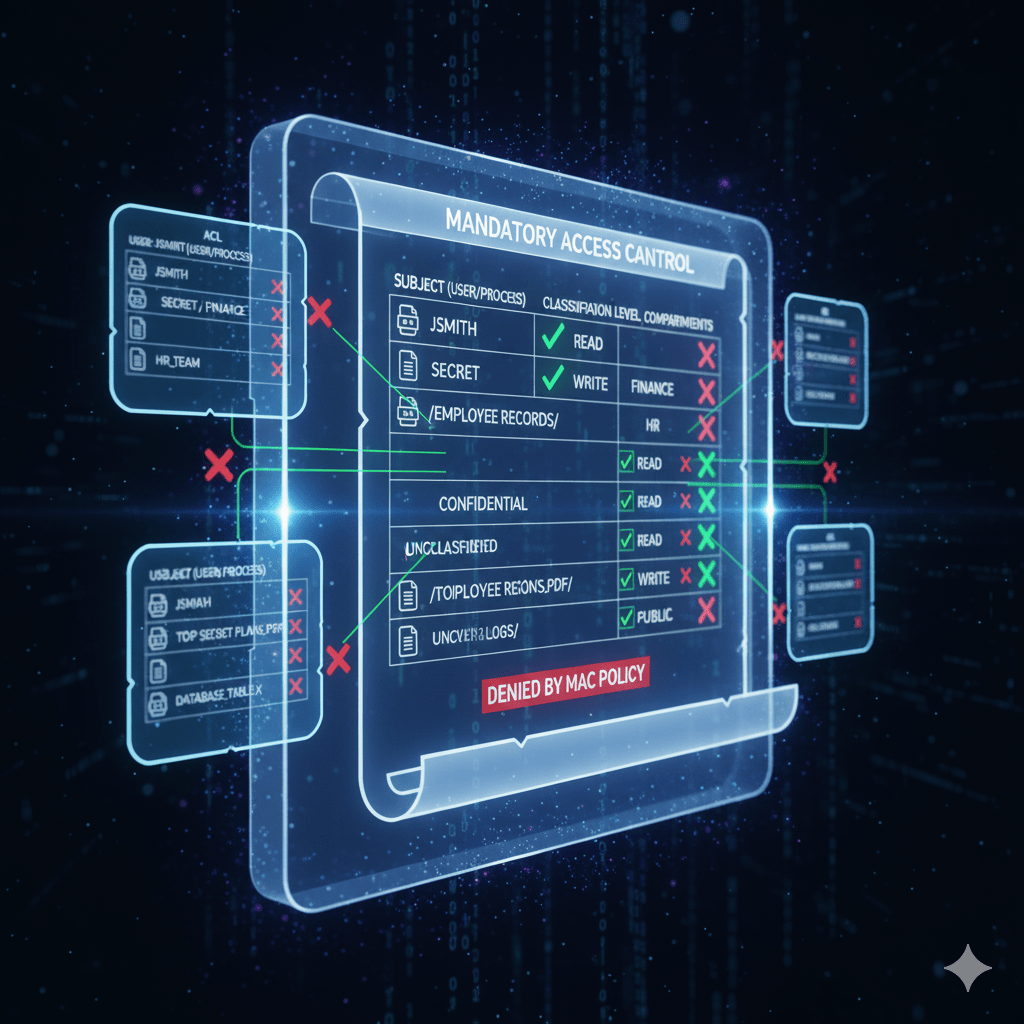
When discussing Authorization Models in SSCP Domain 2: Security Operations and Administration, we explore how systems decide what an authenticated user is allowed to do. While most commercial environments use Discretionary Access Control (DAC), the highest security environments rely on Mandatory Access Control (MAC). MAC is the most rigid and restrictive access control model available. […]
SSCP Day 15: Bridging Trust: Federated Identity and the Magic of SAML, OAuth, and OpenID Connect
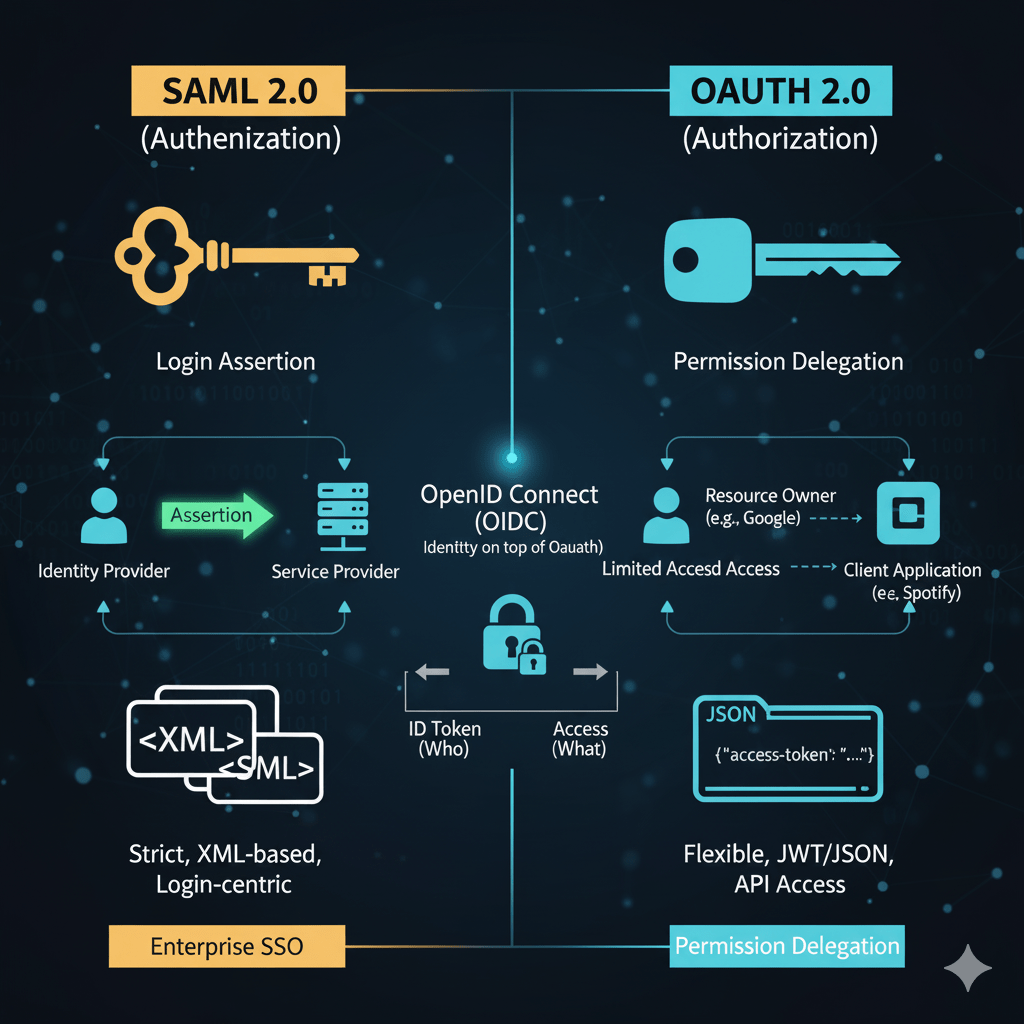
In today’s cloud-centric world, users rarely access applications that all belong to the same company. The core challenge is letting a user log in to one system (like Google) and gain instant, secure access to another system (like Salesforce) without re-entering credentials. This is the goal of Federated Identity. Federated Identity is a crucial concept […]
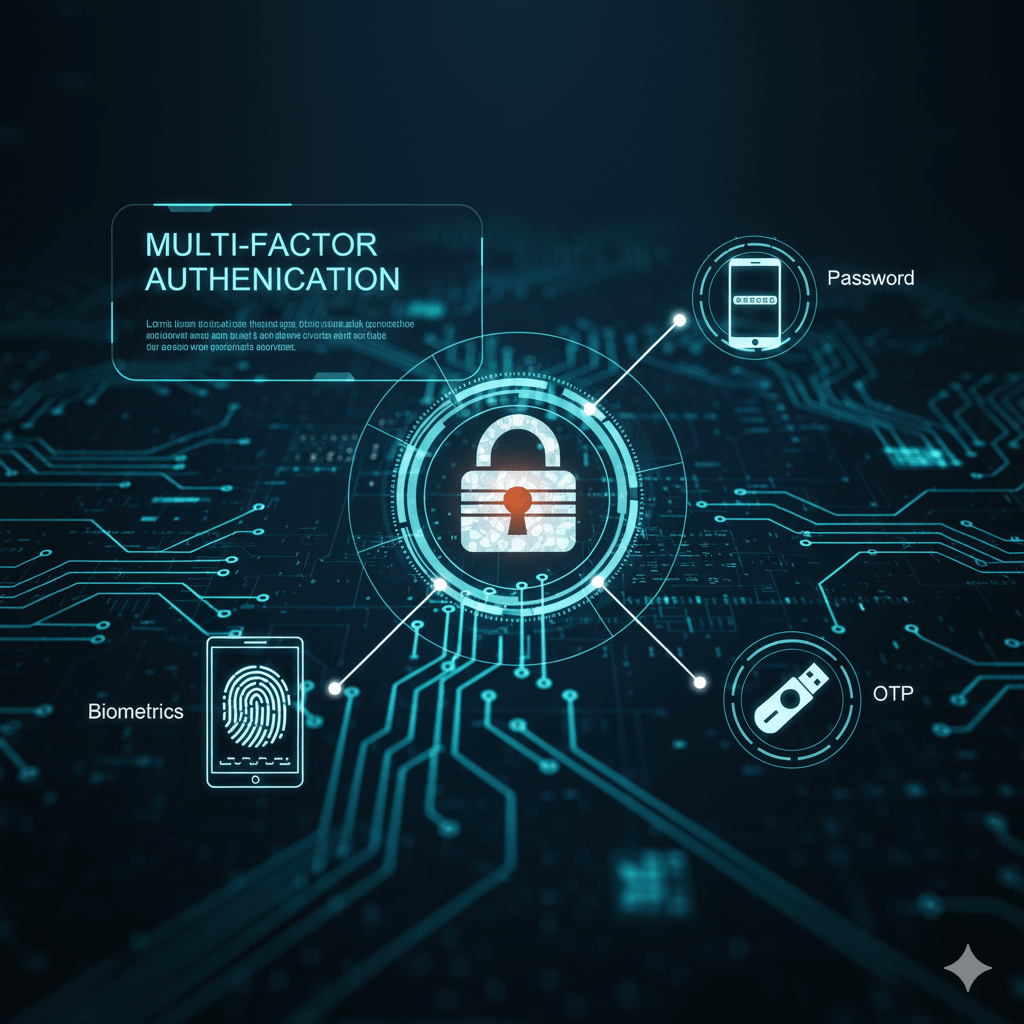
SSCP Day 14: Unbreakable Access: Multi-Factor Authentication and Defense-in-Depth
In modern security, relying on a single authentication method is a guaranteed failure. Multi-Factor Authentication (MFA) is the principle that requires a user to provide two or more distinct categories of credentials before access is granted. This approach is not just a best practice; it is a foundational requirement for Defense-in-Depth within SSCP Domain 2: […]
SSCP Day 13: The Ultimate Key: Biometrics and the Power of “Something You Are”
Moving beyond simple secrets and physical tokens, biometric authentication represents the highest level of assurance in the security world. This is the “Something You Are” factor, relying on the unique, measurable characteristics of an individual to verify their identity. In SSCP Domain 2: Security Operations and Administration, biometrics are covered because they are increasingly deployed […]
SSCP Day 12: Physical Proof: Tokens, Smart Cards, and the Power of “Something You Have”
As we move past the vulnerability of passwords, we encounter the second, more robust authentication factor: Something You Have. This factor ensures that a user must possess a physical object, known as a token, to gain access to a system. In SSCP Domain 2: Security Operations and Administration, understanding these tokens—their types, deployment methods, and […]
From the Server Room to the Living Room: Why I’ve Gone All-In on Linux
There’s a specific kind of magic that happens when professional curiosity meets personal passion. Recently, I’ve been diving deep into the world of Linux through a series of intensive courses on LinkedIn Learning. What started as a move to sharpen my professional toolkit has turned into a complete lifestyle shift—not just for my workstation, but […]
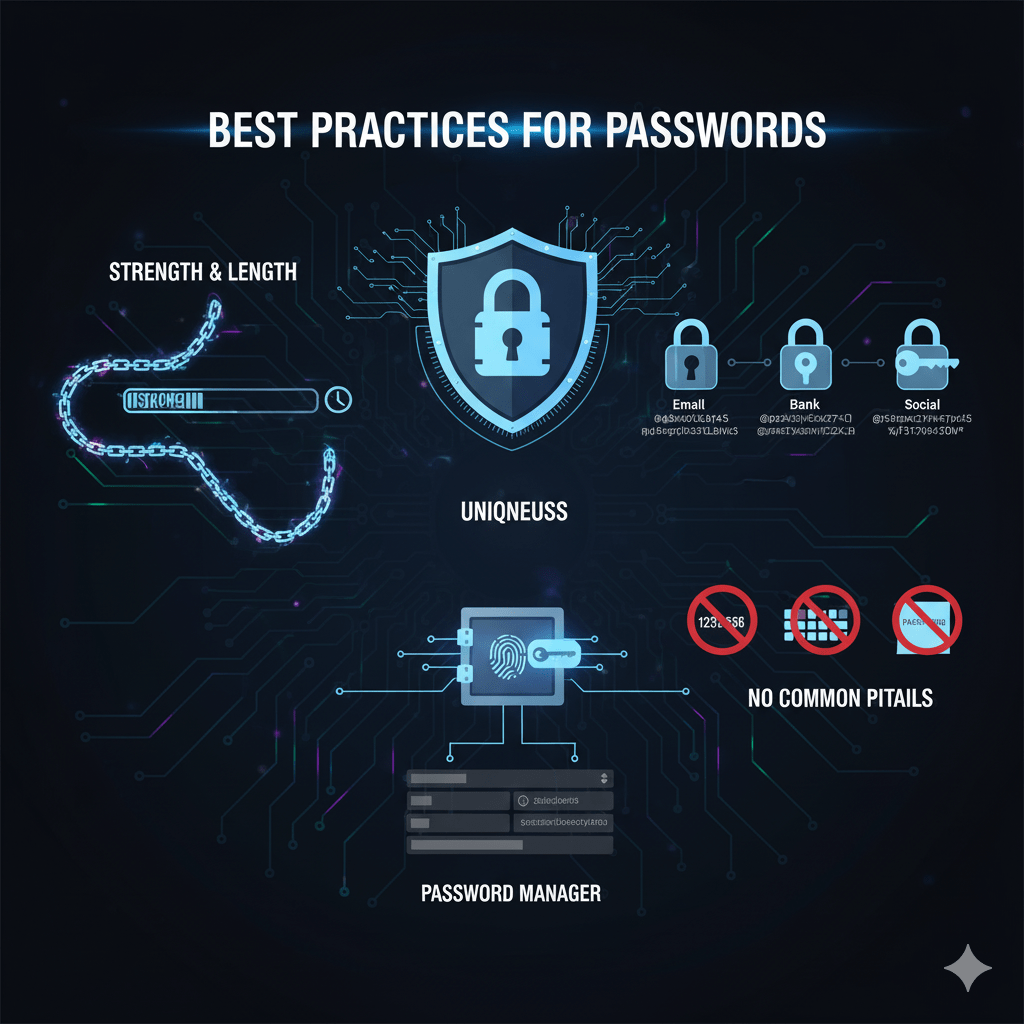
SSCP Day 11: The Foundation of Identity: Passwords and Best Practices
In SSCP Domain 2: Security Operations and Administration, we dive into the technical controls used to manage access. The simplest and most universal control is the first of the three authentication factors: Something You Know. This factor relies on secrets—passwords, PINs, or passphrases—which only the legitimate user is supposed to know. While passwords are the […]
SSCP Day 10: Practice Test
SSCP Domain 1 Practice Quiz SSCP Domain 1 Practice Security Operations and Administration (10 Questions) Loading question… Next Question → Quiz Complete! Restart Quiz