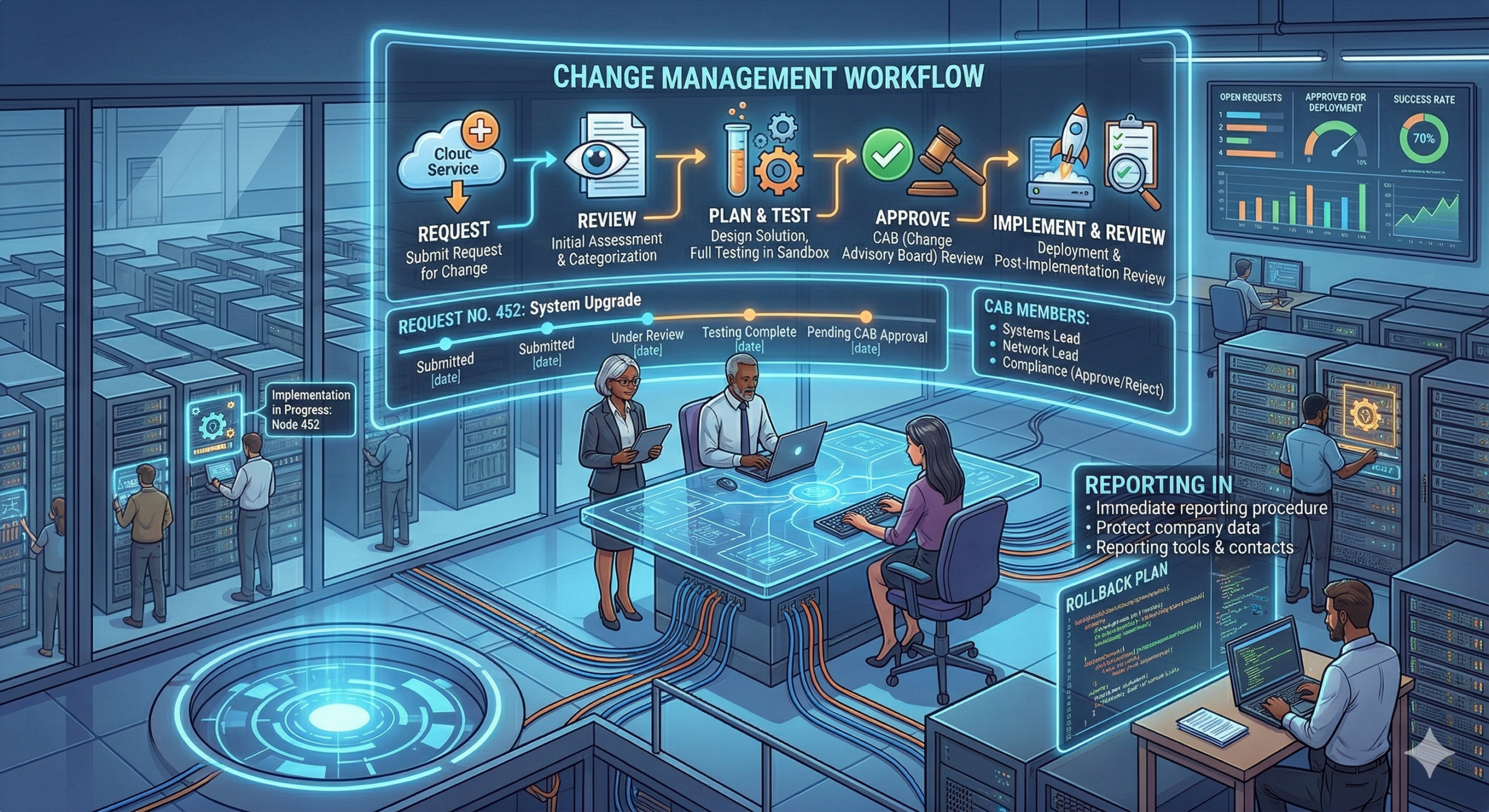
In the world of cybersecurity, stability is key. Every time a system is updated, a firewall rule is modified, or a server is patched, the organization introduces risk. The Change Management Process is the administrative control (Domain 1) designed to minimize this risk by ensuring that all system modifications are documented, reviewed, tested, and approved […]
SSCP Day 2: Beyond Compliance: The Critical Difference Between Security Awareness and Training
For the SSCP, or any security practitioner, understanding human controls is just as important as configuring a firewall. Too often, organizations use the terms “Security Awareness” and “Security Training” interchangeably, but they serve fundamentally different purposes in a robust security program. As an administrative control (Domain 1), your policies must mandate both, but with distinct […]
SSCP Day 1: Who’s Who in Security: Understanding the Core Roles
In cybersecurity, defense isn’t just about firewalls and encryption; it’s about people and processes. Before you implement a single technical control, you need clear administrative controls that define who is responsible for what. This concept, often called separation of duties, is essential for preventing fraud, limiting human error, and ensuring accountability. For the SSCP, you […]
ISC2 SSCP (Systems Security Certified Practitioner) Study Guide
The SSCP certification validates your hands-on ability to implement, monitor, and administer security controls in an IT infrastructure. The exam is highly focused on operational security and technical application. Domain 1: Security Operations and Administration (15%) This domain covers the foundational rules and processes that govern security within an organization. Domain 2: Access Controls (16%) […]
ISC2 SSCP 120-Day Weekday Study Plan
This schedule breaks down the seven SSCP domains and the final review strategy into 120 sessions. The weighting of the domains has been used to approximate the number of days assigned to each area. Day Domain 90-Minute Session Focus Week 1: D1 – Security Operations & Administration (15%) Day 1 D1 Security Roles (CISO, Analyst, […]
Securing the Future of Innovation: I’m Now a Proofpoint Certified AI Data Security Specialist
I am thrilled to announce that I have officially earned my certification as a Proofpoint Certified AI Data Security Specialist 2025! 🎓 As Generative AI (GenAI) continues to reshape the corporate landscape, the intersection of productivity and security has never been more critical. This certification program provided deep, actionable insights into how organizations can harness […]
Leveling Up: My 41-Hour Dive into Cybersecurity Excellence
As the digital threat landscape evolves, staying ahead of adversaries requires more than just curiosity—it requires a structured, rigorous commitment to learning. I recently reached a significant personal milestone by completing a comprehensive series of specialized cybersecurity courses on LinkedIn Learning. Executive Summary 1. The Strategic Core: SSCP & Security Frameworks The cornerstone of this […]
Who Is God? Reflections on the “Great I AM” Devotional
The “Great I AM” devotional emphasizes God’s eternal nature beyond human understanding. It connects the Old Testament’s revelations to Jesus, portraying God as stable amidst life’s changes. This four-day study encourages worship centered on God, highlighting His sovereignty and presence, ultimately fostering deeper faith and trust in His greatness.
From Governance to Hunting: Continuing Education on Modern Cybersecurity Risk and Defense
I recently wrapped up a truly impactful series of four courses on LinkedIn Learning that have fundamentally shifted my perspective on modern cybersecurity. This wasn’t just about collecting certificates; it was a deliberate journey to connect the dots between strategic business governance (GRC), technical risk management, and proactive security operations (Threat Hunting). Here’s a breakdown […]
The Algorithm Wars: Why ECC Dominates RSA in Modern Cryptography
In the foundational layer of digital security, two giants have long battled for supremacy in public-key cryptography: RSA (Rivest–Shamir–Adleman) and ECC (Elliptic Curve Cryptography). Both are essential for securing TLS/SSL connections, digital signatures, and key exchange, but in recent years, ECC has emerged as the clear winner, especially in resource-constrained environments. For security professionals, understanding […]